Partner and vendor exchanges often operate without centralized governance or oversight.

Enterprise Managed File Transfer Without Expanding Your Attack Surface
Enterprise Managed File Transfer designed to replace legacy scripts and aging SFTP servers with centralized automation, governance, and audit-ready visibility.
The Risk Landscape - Why Legacy File Transfer Falls Short
Many organizations still rely on scripts, aging SFTP servers, or loosely governed transfer tools to move critical data. These approaches weren’t built for today’s security, compliance, or operational demands.

Uncontrolled Exposure
Internet-facing transfer servers and flat architectures expand the blast radius of a breach.

Limited Visibility
Siloed systems make it difficult to track who moved data, when it moved, and where it went.

Audit & Compliance Gaps
Inconsistent controls and incomplete records delay audits and complicate investigations.

Operational Fragility
Manual processes and brittle scripts cause failed jobs, delays, and complex recoveries.

Third-Party Risk
What Modern Enterprise MFT Requires
Enterprise file transfer is no longer just about moving files. It’s about doing so with control, accountability, and resilience.
Security by Design
Built-in encryption, strong authentication, and architectures that minimize exposure by default.
Governance & Auditability
Centralized policy enforcement and complete, searchable activity records across all transfers.
Operational Reliability
Automated workflows, intelligent scheduling, and monitoring that ensure consistent execution.
Scalable Partner Exchange
Policy-driven external collaboration that enables growth without increasing risk.
Titan MFT: Secure File Transfer Built for Enterprise Control
Titan MFT is a security-first Managed File Transfer platform designed to support sensitive data movement across complex enterprise environments.
It enables organizations to replace ad-hoc scripts and aging transfer tools with a centralized platform that enforces security policies, maintains visibility, and supports reliable automation across internal systems and external partners.
Titan MFT supports both security and operations teams by combining governance, resilience, and flexible deployment into one controlled transfer environment.
Titan MFT: Secure File Transfer Built for Enterprise Control
Titan MFT centralizes and secures automated file workflows across on-prem, cloud, and hybrid environments.
It replaces disconnected scripts and isolated transfer servers with policy-driven automation, full visibility, and resilient architecture designed for regulated enterprises.
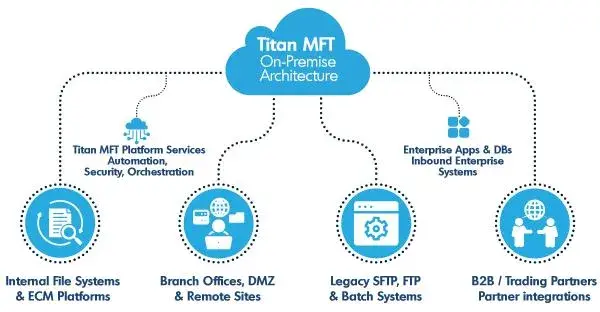
Architecture That Supports Control Not Just Connectivity
Deploy Titan MFT in on-premises, hybrid, or cloud-aligned environments while maintaining consistent security and governance controls.
Architect transfer workflows so external access is isolated from core systems, helping reduce exposure and limit lateral movement risk.
Integrate inspection and policy controls into file transfer paths to help ensure sensitive data is handled according to organizational requirements.
Capture detailed transfer activity and export logs to SIEM and monitoring systems to support oversight, investigations, and audit readiness.
Security & Governance, Without Operational Drag
Titan MFT balances strong security controls with the operational reliability teams need to keep data moving.
- Encrypted data in transit and at rest
- Role-based access and least-privilege controls
- Centralized, audit-ready logging
- Policy-driven partner and user access
- Integration with monitoring and security tools
Ideal Use Cases for Titan MFT
Secure System-to-System Workflows
Automate reliable transfers between internal applications, databases, and platforms.
Governed Partner Exchange
Share files with vendors, customers, and third parties using controlled, auditable processes.
Batch Processing & Scheduled Jobs
Support high-volume, time-sensitive file exchanges with predictable automation.
Regulated Data Movement
Move sensitive data with the controls and visibility required in regulated environments.
Hybrid Cloud File Workflows
Securely move files between on-prem systems and cloud environments without losing governance.
Assess the Security and Resilience of Your File Transfer Environment
A structured evaluation helps identify architectural exposure, governance gaps, and operational weaknesses before they impact security, compliance, or business continuity.
How Titan MFT Solves It
Our subscription model delivers enhanced value while providing the flexibility and predictability modern enterprises demand.
Legacy Scripts & Manual Processes
Compliance & Security Gaps
Limited Integration Capabilities
Operational Complexity
Core MFT Capabilities
Automated File Workflows
Build Complex, Policy-Driven Workflows Without Code
Pre- and post-processing capabilities including zip, encrypt, decrypt, and custom scripts
Intelligent failover with automatic retries and conditional branching logic
Multi-destination delivery for simultaneous file distribution
Template-based job creation for rapid deployment across teams
Enterprise Security, Compliance & Governance
On-Premise Security & Governance Controls
Encryption & Digital Signing
PGP encryption and digital signing within your controlled environment (add-on module)
Malware & Content Inspection
ICAP-based malware scanning and data loss prevention with content inspection
Access Control & Governance
Role-based administrative access with granular permissions integrated with enterprise IAM
Audit, Logging & Monitoring
Syslog-based centralized logging for auditability and operational visibility
Enterprise Connectors
File Transfer Protocols
Full support for SFTP, FTPS, and FTP with advanced authentication, key management, and protocol-level security controls
Object Storage & Hybrid Destinations
Native support for Amazon S3 and S3-compatible endpoints, enabling controlled integration with object storage platforms while maintaining on-premise governance and security policies.
Collaboration Platforms
Direct integration with enterprise collaboration and content platforms such as SharePoint, Synology, and Google Drive-supporting governed document workflows across internal and external systems.
On-Premises Systems
UNC path and local file system support for legacy infrastructure, private environments, and DMZ architectures.

Built for Environments Where Security and Reliability Matter
Titan MFT supports organizations operating in regulated, high-reliability environments where file transfer is critical to daily operations. Deployments emphasize stability, governance, and long-term operational confidence.
Resources
Titan MFT Overview
Security & Compliance Guide
Architecture & Deployment Overview
MFT Best Practices
Download The Titan MFT One Pager
Get a concise overview of how Titan MFT enables secure, governed file exchange with enterprise-grade visibility and compliance alignment.
- Segmented, security-first architecture
- Centralized logging and audit visibility
- Fast deployment with flexible integrations
Trusted by 30,000+ organizations worldwide
Want the Full Product Overview?
Download the Titan MFT one-pager for technical and business details.
Gated form • Instant download after submission
Titan MFT Add-On Modules
Extend Titan MFT with specialized modules that enhance security, compliance, and intelligence capabilities. Deploy anywhere-from on-premises infrastructure to leading cloud platforms.

High Availability Scaling Module
Active-active clustering and failover to eliminate single points of failure.

FIPS Compliance Module
Enforce FIPS-aligned cryptographic standards for regulated environments.

Advanced Encryption Module
File encryption, decryption, and digital signing for regulated workflows.

Neo AI Assistant Module
Operational insights and intelligent exception monitoring.
G2 Awards of Managed File Transfer (MFT) Software
_UsersMostLikelyToRecommend_Mid-Market_Nps.png)
_EasiestToDoBusinessWith_Mid-Market_EaseOfDoingBusinessWith.png)
_BestUsability_Mid-Market_Total.png)
_EasiestSetup_Mid-Market_EaseOfSetup.png)
How Titan MFT Solves It
Zero-Code Automation
Replace legacy scripts and manual processes with drag-and-configure job creation, advanced orchestration controls, and intelligent workflow management.
Enterprise Connectors
Native connectors for virtually any system eliminate integration barriers - SFTP, FTPS, Amazon S3, SharePoint, Google Drive
Security & Compliance
Built-in PGP encryption, digital signing, integrity checks, and comprehensive audit trails ensure compliance with HIPAA, PCI, SOX, and FedRAMP requirements.
Intelligent Administration
Rapid Azure/AWS Marketplace deployment, centralized admin interface, and automated job orchestration with event-based or scheduled execution.
Complete Visibility
End-to-end auditability with job history dashboards, success/failure tracking, error details, and comprehensive logging for governance and troubleshooting.
Pricing & Deployment Options
Titan MFT Server is available via the traditional, on-premise licensing model. Simply purchase the license and you can download the software to install in whatever environment best meets your requirements.
Need a custom configuration or enterprise volume licensing?
Pre-configured Marketplace deployments across leading cloud providers.
Need a custom configuration or enterprise volume licensing?
Benefits at a Glance
Accelerated Deployment
Deploy quickly via Azure or AWS Marketplace with guided onboarding and minimal operational overhead.
Strengthened Compliance
Built-in security controls and comprehensive audit trails ensure adherence to regulatory requirements across industries.
Operational Excellence
Eliminate custom scripts and manual file handling with scalable, no-code automation that reduces operational drag.
Reduced Infrastructure
Consolidate file transfer infrastructure into a single, secure, scalable engine that replaces multiple legacy solutions.
Future-Ready Architecture
Modular platform with optional AI intelligence layer (Titan Neo) and flexible connectors that scale with your business.
Real-World Use Cases
Healthcare Systems
Secure patient data exchange with HIPAA-compliant encryption and comprehensive audit trails.Financial Services
Automated transaction processing and regulatory reporting with PCI compliance and fraud protection.Government Agencies
FedRAMP-ready environments with enhanced security controls for sensitive data movement.Manufacturing
Partner data exchange and supply chain automation with reliable, secure file transfer workflows.Technical snapshot
Protocols & Platform
SFTP, FTPS, HTTPS, WebDAV/S, RESTful API support on Windows Server 2016+ and Linux VMs with .NET Core architecture.
Security & Architecture
Reverse-proxy with zero inbound ports, FIPS 140-2 encryption, DDoS protection, IP banning, and policy-based control.
High Availability
Active/Active or Active/Passive clustering with Titan MFT, web-based React UI with live traffic monitoring.
Cloud Deployment
Pre-configured VM images for Azure, AWS, Google Cloud with 2.0 GHz multi-core CPU, 8 GB RAM requirements.
Enterprise success stories
Titan MFT transformed our file transfer infrastructure overnight. We eliminated dozens of custom scripts, achieved SOX compliance, and reduced our operational overhead by 60%. The Azure Marketplace deployment was seamless, and we were transferring files securely within hours.
— IT Director
Fortune 500 Manufacturing Company
Titan MFT is solid, flexible, and reliable. The software is highly configurable-we’ve made it do nearly everything we need it to.
— John C
Technology
We began experiencing immediate improvements. Titan MFT’s design gave us stronger security and helped us meet regulatory demands.
— Fred Curry
Dir. of Info Security Children’s National Hospital
Support has been phenomenal. Their team helped us rigorously test and meet our implementation goals with zero delays.
— Dave McCabe
Director of Data Center Operations, Datalogix
SRT is fantastic when it comes to development and product continuation. You feel like you’re part of the roadmap.
— Benjamin Weiss
IT Infrastructure Admin, SYNLAB
Professional Services
SRT offers professional services, delivered by remote streaming session.
Professional Services are offered in discounted packages or at an hourly rate. Customers with Business Standard or Premium Support receive discounts on all Professional Services.
Deployment Package
- Planning and Analysis
- Install and Setup
- Outcome Verification - Validation that the deployment or migration was completed successfully and the environment is functioning as expected (configuration, connectivity, permissions, workflows, etc.).
- Outcome Verification Report - A detailed report documenting the verification process, actions performed, and confirmation that the environment is operating correctly.
- Basic Training (1 HR Max)
- Consult and Setup Report
- Outcome – Verification Report
Migration Package
- SRT Application Migrations
- Migrate to/from On-Prem, Cloud, or HA
- Outcome Verification - Validation that the deployment or migration was completed successfully and the environment is functioning as expected (configuration, connectivity, permissions, workflows, etc.).
- Outcome Verification Report - A detailed report documenting the verification process, actions performed, and confirmation that the environment is operating correctly.
- Admin Training (1 HR Max)
- Consult and Migration Report
- Outcome – Verification Report
Checkpoint Package
- Application Performance Assessment
- Configuration and Environment Review
- Best Practices Evaluation
- Software Upgrade/Maintenance
- Findings and Remediation Report
- Optimization Recommendations
