Secure File Transfer for Banking & Financial Services
Secure File Transfer & Managed File Transfer for Banks, Financial Institutions, and Insurance Providers
Security-first file transfer architecture designed for regulated financial data - supporting operational resilience, regulatory compliance, and audit-ready governance across complex financial ecosystems.
Industry Data Movement Reality
Banking, financial services, and insurance organizations rely on file-based data exchange to operate core business functions and meet regulatory obligations.
Despite modernization efforts, file-based transfer remains foundational infrastructure. These exchanges are not legacy plumbing - they are mission-critical pathways connecting financial institutions to markets, regulators, and partners.
As a result, financial institution data transfer security and regulated data transfer banking infrastructure have become core priorities for security and compliance teams.
Financial institutions face increasing regulatory pressure and security risks when transferring sensitive data across systems and partners.
Across BFSI environments, file transfer underpins:
Financial institutions depend on secure file transfer infrastructure to move critical operational and regulatory data every day. These exchanges connect internal banking systems, payment networks, regulators, and third-party partners.
-
Payment, settlement, and clearing files exchanged with networks and counterparties
-
Reconciliation and end-of-day batch processing
-
Regulatory and supervisory reporting submissions
-
Customer, account, and policy data movement between internal systems
-
Data exchange with fintechs, vendors, processors, and service providers
Key Industry Risks in File Transfer

Systemic Exposure
File transfer services often sit at the edge of financial environments. Because they connect internal systems with external networks and partners, they are persistent targets for external probing and internal misuse.
Poorly segmented architectures can turn routine data exchange into broad exposure across financial systems.

Third-Party & Vendor Ecosystem Risk
Banks and insurers exchange data with hundreds of counterparties, fintech partners, clearing firms, and service providers.
Each connection expands the surface area that must be governed, monitored, and controlled across the organization’s data ecosystem.
Without clear governance and access controls, third-party connections can become uncontrolled pathways into sensitive financial environments.

Audit & Examiner Scrutiny
Financial institutions must demonstrate clear control over how sensitive data moves through their systems.
Security and compliance teams must be able to answer key questions during audits and examinations, including:
- Who accessed sensitive data
- When files were transferred
- How data integrity was preserved
Gaps in visibility, logging, or reporting create operational friction and increase risk during regulatory reviews.

Operational Resilience Risk
Many critical financial processes depend on reliable file-based workflows.
Settlement files, reconciliation reports, and regulatory submissions often move through scheduled batch transfers across multiple systems.
Failures in these workflows can delay downstream processing, disrupt internal operations, and impact customer-facing services.
Resilient file transfer infrastructure is therefore essential for maintaining operational continuity under stress.
How SRT Secures File Exchange for BFSI
South River Technologies approaches financial file transfer as controlled infrastructure rather than a standalone tool. The platform is designed to support secure data exchange across internal systems, counterparties, and regulated environments while maintaining strong governance, visibility, and operational continuity.
SRT’s Titan platform enables secure file transfer for banks and supports secure file transfer workflows across complex financial ecosystems, including managed file transfer financial services environments.
Architectural Principles
Segmented Deployment Architecture
DMZ-based deployment separates internet-facing access from internal transfer systems, reducing systemic exposure. Learn more about segmented deployment / DMZ.
Centralized Logging & Monitoring
Comprehensive event logging supports SIEM integration, incident investigation, and operational oversight.
Policy-Driven Data Movement
Centralized policies govern how sensitive financial data is accessed, transferred, and retained across partner ecosystems.
Partner Access Governance
Controlled third-party connectivity enables secure exchange with fintech partners, clearing networks, and vendors.
Resilient Processing
Replay support and automation capabilities ensure settlement, reporting, and batch workflows complete reliably.
This approach prioritizes containment, visibility, and control - supporting secure data movement without expanding exposure.
Industry Use Cases
Common BFSI operational scenarios supported by SRT include:
Secure exchange of payment and settlement files with clearing networks
Clearing, reconciliation, and end-of-day batch workflows
Regulatory and supervisory reporting data transfers
Controlled data exchange with fintechs, processors, and third-party vendors
Data feeds supporting risk modeling, analytics, and reporting platforms
Secure data exchange with regulators and supervisory bodies (e.g., reporting submissions to central banks or financial regulators)
Compliance & Audit Readiness
Financial institutions are expected to produce clear, defensible evidence of control over sensitive data movement during audits, examinations, and incident investigations.

SRT supports alignment with regulatory and supervisory expectations by helping organizations maintain centralized visibility, access control, and logging across file-based data exchange.
Financial institutions use SRT to support alignment with:
- GLBA Safeguards expectations
- FFIEC-informed security and risk management practices
- SOX requirements where applicable
- PCI DSS considerations where payment card data is involved
- NIST cybersecurity framework guidance
- ISO 27001 information security standards
This supports faster evidence collection, clearer accountability, and reduced operational friction during regulatory and internal reviews.
Why BFSI Security Teams Choose SRT
Security and IT leaders in BFSI choose SRT when they need to move regulated data without expanding their attack surface.
They value:
Security Architecture
A security-first architecture designed for regulated financial systems
Segmented Deployment
Segmented deployment architectures that limit blast radius and reduce internet-facing exposure
Ecosystem Governance
Governance over complex partner ecosystems
Audit Visibility
Strong audit visibility designed to support examiner, risk, and compliance review processes
Regulatory Alignment
Solutions built for audit-intensive, regulator-aware environments
Operational Automation
Reliable automation supporting settlement, reconciliation, and reporting workflows
SRT is designed to operate reliably behind the scenes - supporting critical workflows without introducing unnecessary risk.
How Financial Institutions Use SRT
Financial organizations rely on SRT for:
- Mission-critical settlement and clearing workflows
- Long-running automated file exchange pipelines
- Secure third-party data exchange with fintech ecosystems
Secure Financial Data Workflows
How Financial Institutions Manage Secure Data Transfer
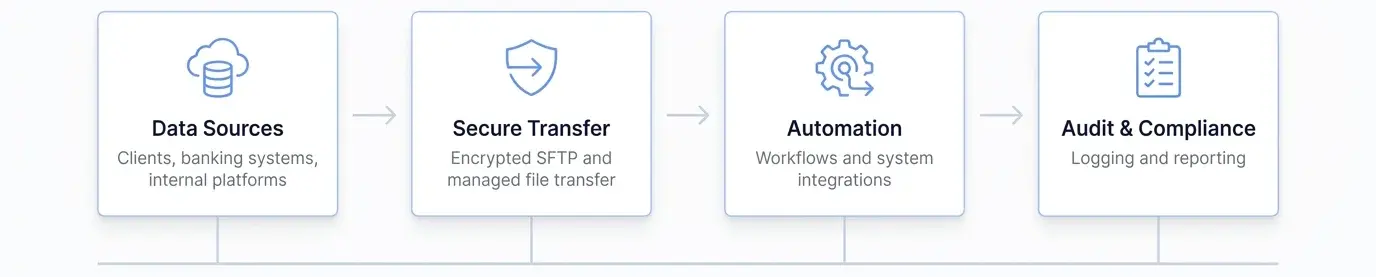
Financial institutions rely on secure file transfer solutions to support critical operations across internal systems, customers, and third-party partners. These workflows require security, automation, and auditability to meet regulatory and operational requirements.
- Secure client document exchange
- Automated transaction and trading data transfers
- Regulatory reporting and audit file delivery
- Third-party and vendor data exchange
Built for Financial Compliance
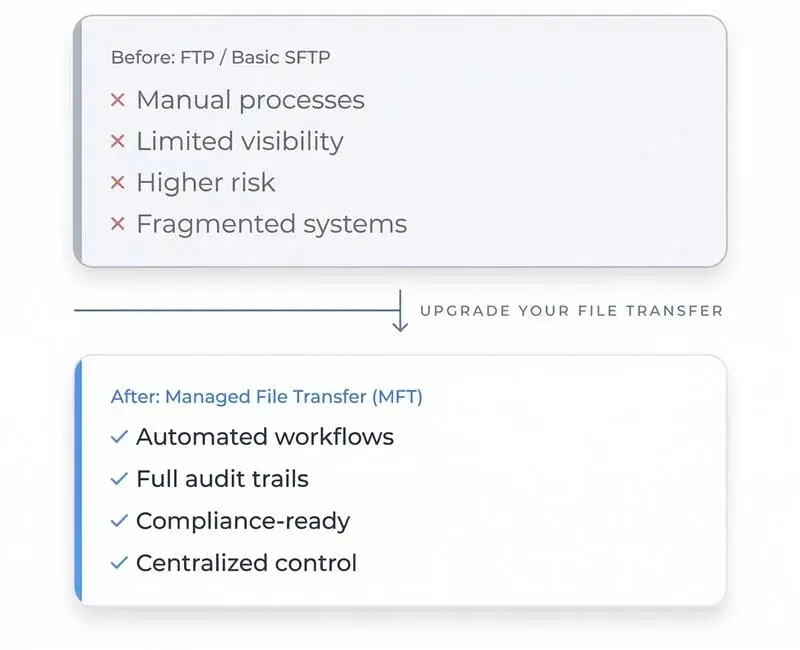
Why Financial Institutions Choose Managed File Transfer
Secure Your Financial Data Transfers with Confidence
Protect sensitive financial data, meet compliance requirements, and streamline file transfer operations.
